It’s hard to ignore the rise of phishing scams these days. They seem to pop up in our inboxes with alarming frequency. As we become more aware of these deceptive tactics, scammers are also upping their game, using increasingly sophisticated methods to lure in unsuspecting victims.
One particularly sneaky tactic involves impersonating a help desk or support team. You might receive an email claiming that your Microsoft 365 account is set to expire today.
The goal? To create a sense of panic and urgency, prompting you to act quickly without thinking. So, how do you recognize these scams and protect yourself from falling victim to them? Let’s go down that road to keep you safe.
I’M GIVING AWAY A $500 GIFT CARD FOR THE HOLIDAYS

A woman opening email on laptop (Kurt “CyberGuy” Knutsson)
How can you tell if it is a scam email?
It’s easy to see why people fall prey to these sorts of tactics, because scammers do a relatively good job of making these scam emails appear professional and legitimate. They go as far as to change the contact information of the email sender to something legitimate like an actual helpdesk or IT department or business.
Upon further examination of the email sender’s contact information, you can see that the domain address of the actual email address is different and random. For example, the name in the “From” field of the email may read from helpdesk, but if you click on the contact information to view the email address, it will have a domain from @magicpin.in, @gmail.com or @hotmail.com, etc. If it’s an email supposedly from Microsoft, you’d expect the domain to be microsoft.com.
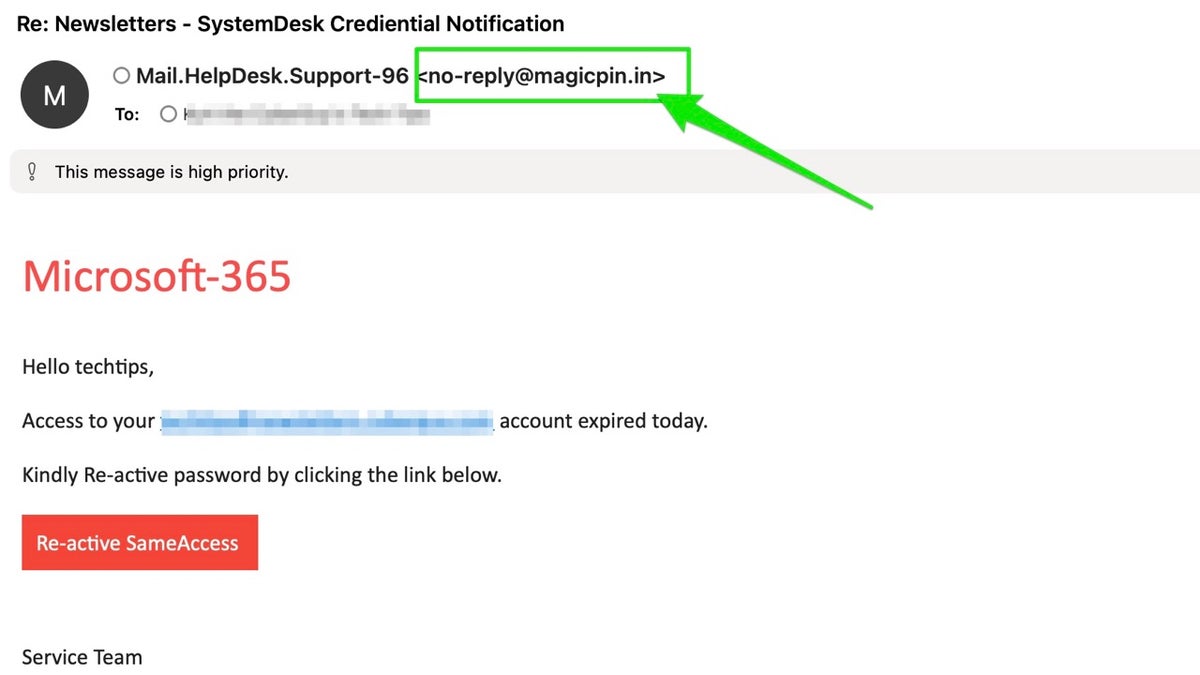
Microsoft scam email (Kurt “CyberGuy” Knutsson)
DON’T CLICK THAT LINK! HOW TO SPOT AND PREVENT PHISHING ATTACKS IN YOUR INBOX
How are victims exploited by these types of scams?
Getting a “fake” email may seem relatively benign, but it can be a slippery slope to identity theft and fraud. Below are ways in which scammers take advantage of their victims with these phishing email scams:
1. Email validation: By opening the email or engaging with the email (clicking a link or responding to it), you can validate that the email account they messaged is active. Oftentimes, scammers randomly email people whose email address they’ve gotten from data breaches, the dark web or data harvesting.
2. Information gathering: If you reply to the email or use any other contact information they provide to “reinstate” your account, it will validate that the email address they reached out to is active, and they will likely hard-sell you for financial and personal information. If you call any phone number they provide you, they will also connect your phone number with your email address so they can continue to update their information on you.
3. Malware distribution: They will often have buttons, links or attachments included in the email. If you click the attachment, it can download malware or a virus to your device. If you click on a link that’s provided in the email, it might take you to a website that will collect your personal and financial information or download malware or viruses to your device.
CLICK HERE FOR MORE US NEWS

Illustration of scammer at work
SNEAKY SCAMMERS DRAIN BANK ACCOUNT IN SINISTER PHONE PHISHING SCHEME
What should you do if you receive these types of phishing emails?
There are a few easy steps you can take if you receive an email you suspect is a phishing scam.
1. Do not click on any links or buttons and do not download or open any attachments: This helps prevent malware installation and protects your personal information. The best way to safeguard yourself from malicious links that install malware, potentially accessing your private information, is to have antivirus software installed on all your devices. This protection can also alert you to phishing emails and ransomware scams, keeping your personal information and digital assets safe. Get my picks for the best 2024 antivirus protection winners for your Windows, Mac, Android and iOS devices.
GET FOX BUSINESS ON THE GO BY CLICKING HERE
2. Do not reply or reach out to these scammers by email or phone: Engaging with them can confirm your email address is active, leading to more scams.
3. If your email client allows it, you can block the sender and report it as a phishing email: This action helps protect yourself and others by alerting your email provider to malicious activity.
4. Verify the email’s legitimacy by checking the official website of the organization: Directly accessing your account ensures you receive accurate information without falling for fake notifications.
5. If two-factor authentication is offered for your account, enable it: 2FA adds an extra layer of security, making it harder for scammers to gain access even if they have your password.
6. Invest in personal data removal services: Reducing your digital footprint minimizes the risk of identity theft and scams based on harvested data. While no service promises to remove all your data from the internet, having a removal service is great if you want to constantly monitor and automate the process of removing your information from hundreds of sites continuously over a longer period of time. Check out my top picks for data removal services here.
HOW TO STOP PROMOTIONAL EMAILS WHERE YOU CAN’T UNSUBSCRIBE
Kurt’s key takeaways
Phishing scams are becoming increasingly sophisticated, but staying informed and vigilant can significantly reduce your risk. By adopting good digital habits and following the tips we’ve shared, you can navigate the online world with confidence. Remember, awareness is your best defense, so keep sharing this knowledge with friends and family to help protect everyone from these deceptive tactics.
What’s the most unusual or clever phishing attempt you’ve encountered, and how did you recognize it as a scam? Let us know by writing us at Cyberguy.com/Contact.
CLICK HERE TO GET THE FOX NEWS APP
For more of my tech tips and security alerts, subscribe to my free CyberGuy Report Newsletter by heading to Cyberguy.com/Newsletter.
Ask Kurt a question or let us know what stories you’d like us to cover.
Follow Kurt on his social channels:
Answers to the most asked CyberGuy questions:
New from Kurt:
Copyright 2024 CyberGuy.com. All rights reserved.

